In the realm of digital security, knowing how to tell if someone is accessing your iPhone remotely is a pivotal skill. This guide sheds light on the subtleties of remote intrusions and offers pragmatic advice to bolster your iPhone’s defenses.
Understanding Remote Access: A Closer Look
The possibility of remote viewing and control over an iPhone isn’t merely speculative; it’s a tangible threat in today’s interconnected world. With advancements in technology, what was once considered borderline science fiction is now a sobering reality. This capability, while offering numerous benefits in terms of accessibility and convenience, also opens up a Pandora’s box of security vulnerabilities.
Recognizing the Signs of Remote Access
Vigilance is your first line of defense against unauthorized remote access. Several indicators should prompt further investigation:
- Unusual Battery Drain: A sudden decrease in battery life could signal background activities related to malicious access.
- Surge in Data Usage: An unexplained increase in data consumption may indicate remote operations running on your device.
- Strange Background Noises: Odd sounds during phone calls can be a sign of eavesdropping.
- New Programs or Settings: Unexpected changes in your iPhone’s configuration could be the work of an intruder.
- Unknown Accounts: Be wary of new, unfamiliar accounts linked to your device, suggesting potential breaches.
- Performance Issues: A sluggish or unresponsive iPhone might be under the control of a remote operator.
These symptoms, while not exhaustive, are strong indicators of compromise. Early detection is crucial to mitigating potential damage.
Steps to Reinforce Your iPhone’s Security
Protecting your iPhone from unauthorized remote access involves both preventive measures and reactive strategies. Here’s how you can fortify your digital fortress:
- Update Regularly: Keeping your iOS and apps up to date is critical in patching security vulnerabilities.
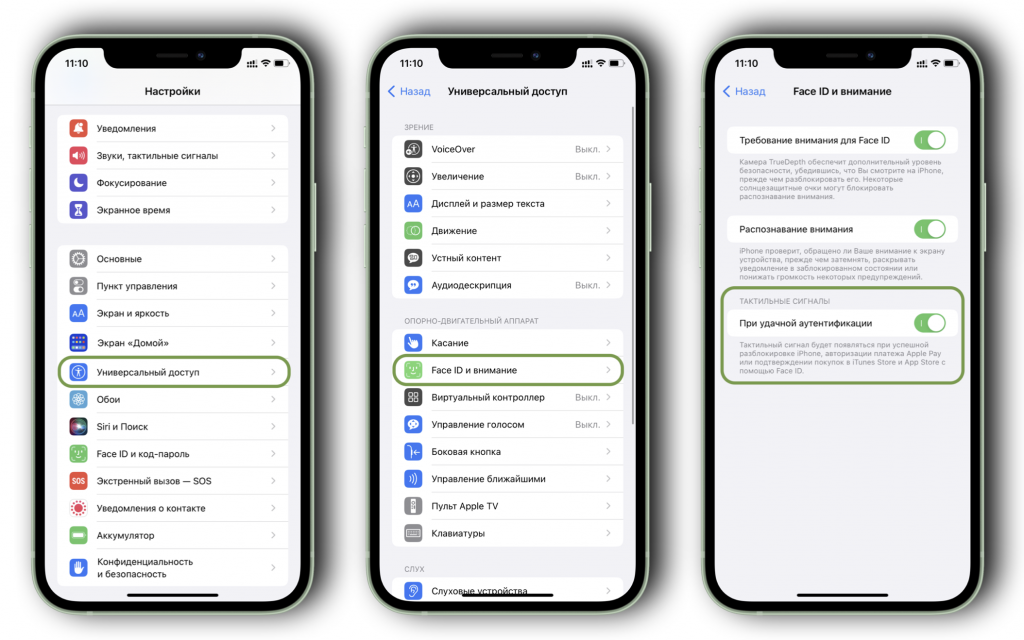
- Strong Authentication: Employ complex passwords and enable multi-factor authentication wherever possible.
- Limit App Permissions: Restrict the access rights of apps to only what is necessary for their function.
- Be Wi-Fi Wary: Avoid using public Wi-Fi networks without a VPN to shield your data from prying eyes.
Empowerment Through Awareness
In the battle for digital privacy, knowledge is your greatest weapon. By familiarizing yourself with the hallmarks of remote access and adopting a proactive stance on security, you can significantly reduce the likelihood of your iPhone becoming an open book to unauthorized users. Remember, in the digital arena, complacency is the enemy of security.
Final Reflections: Vigilance is Key
In concluding our exploration of iPhone security, let’s underscore the importance of vigilance. The digital landscape is fraught with challenges, but through awareness and actionable knowledge, we can navigate it safely. Protecting your iPhone from remote intrusions isn’t just about securing a device; it’s about safeguarding your digital life.
FAQs: Enhancing Your iPhone’s Security
Q: How can I check for unauthorized devices linked to my iPhone?
A: Regularly review your Apple ID and iCloud accounts for unknown devices. Remove any device that doesn’t belong to you.
Q: What should I do if I suspect my iPhone has been accessed remotely?
A: Change your passwords immediately, update your iOS, and consider a factory reset after backing up your data.
Q: Can antivirus software detect remote access on my iPhone?
A: While iOS is designed to be secure, some third-party security apps can provide additional monitoring and alerts for suspicious activities.
Q: How often should I update my iPhone and apps?
A: Always install iOS updates as soon as they’re available. Regularly check for app updates to ensure all security patches are applied.
